Why HID Amico is Revolutionizing Biometric Security in the GCC
The Future of Access Control is Your Face
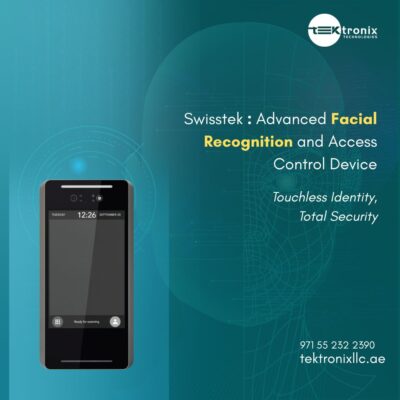
The HID Amico isn't merely another reader. It's an advanced identity verification platform that uses your face as the most secure, reliable, and convenient credential. For security managers in Dubai, facility managers in Riyadh, and government officials in Abu Dhabi, this represents a paradigm shift from the credential you carry to who you are.
Discover The Amico Revolution
Ready to explore the future of access control? Book a live demonstration of HID Amico with a Tektronix security professional today.
Schedule Your Live DemoThe Technical Superiority of HID Amico: A Deep Dive
What makes HID Amico distinct from other biometric devices is its sophisticated design and enterprise grade technology, specifically engineered to withstand the demanding environments of the GCC.
1 Advanced Facial Recognition Algorithm & Liveness Detection
At its core, the HID Amico Reader utilizes a powerful on device facial recognition algorithm that goes far beyond simple facial mapping. It employs 3D depth sensing and infrared technology to build precise biometric templates, ensuring accurate authentication even in challenging lighting conditions common in the GCC. From harsh midday sun to dimly lit parking garages. Additionally, its advanced Liveness Detection technology prevents spoofing attempts using photos or videos, a crucial feature for high security facial recognition systems protecting sensitive sites.
2 Seamless Integration & Multi Technology Support
One of HID Amico's greatest strengths is its ability to function as a unified security hub. As an HID Mercury based reader, it seamlessly integrates with existing access control systems, protecting your infrastructure investment. It supports HID's SEOS Technology, mobile credentials via Bluetooth, and traditional card credentials all in one device. This enables gradual migration to facial recognition or implementation of robust multi factor authentication. For instance, requiring both face and mobile credential to access server rooms in oil and gas facilities.
3 Engineered for GCC Environments
The HID Amico is built to last and perform in conditions unique to the Middle East. The hardware is designed to withstand high ambient temperatures and is dust resistant, ensuring operation in environments where other readers might fail. This makes it ideal for diverse applications. From elegant corporate towers in Dubai to exterior doors of government buildings in Saudi Arabia.
Explore Technical Specifications
How does Amico's on device processing guarantee privacy and speed? Dive deep into its technical architecture and enterprise capabilities.
View Technical DocumentationTransforming Security Across GCC Sectors
The versatility of HID Amico makes it the perfect solution for the diverse security requirements prevalent across the region.
Secured Corporate Environments
In financial districts like Abu Dhabi and Doha, Amico enables touchless facial recognition access control that streamlines employee flow during peak hours while maintaining precise records of who accessed which areas and when.
Critical Infrastructure
For oil and gas security, Amico's robust design and high assurance capabilities help protect remote and sensitive sites by integrating with existing video intercom systems for visual verification.
Gated Communities & Hospitality
The device delivers both security and a seamless, modern experience for residents and VIP guests, supporting wireless remote access control for corporate buildings and luxury residences.
The Tektronix Advantage: More Than Just a Distributor
Choosing Tektronix as your HID Amico distributor means gaining a true partner. We offer comprehensive support. From initial system design and HID Amico installation through ongoing maintenance ensuring your investment is backed by expertise, reliability, and exceptional value.
The Future of Access is Facial
The transition to facial recognition isn't just a technological upgrade. It's a step toward a more secure, efficient, and intelligent future. The HID Amico Face Recognition device, backed by Tektronix's regional expertise, offers a transformative solution that addresses the unique challenges facing the GCC market.
It's time to leave behind outdated systems and embrace the credential you always carry. Your face.
Get a Customized Quote for Your Facility
Ready to transform your access control? Contact Tektronix Technology today for a personalized consultation and quote for HID Amico, tailored to your specific security needs across Dubai, Riyadh, Abu Dhabi, and the entire GCC region.
Request Custom Quote Contact Tektronix TechnologyYour face is your credential. Your security is our mission.